DefenseCraft
Cybersecurity
Our Philosophy
Cybersecurity is not a product that can be purchased, nor is it an IT specific function. It’s a continuous organization wide process of education and technological improvement.
Our Mission
To develop an organization wide security aware mindset melded with carefully crafted policy and robust security controls.
Professional Services
Design
- Governance Frameworks
- Network Architecture
- Security Controls
- Policy Development
Testing
- Vulnerability Assessment
- Penetration Testing
- Compliance Audits
- Social Engineering
Risk Management
- Risk Assessment
- Compliance Strategy
- Contingency Planning
- Supply Chain Protection
Training
- Security Awareness Training
- Social Engineering Defense
Superior security strategies from leading-edge research
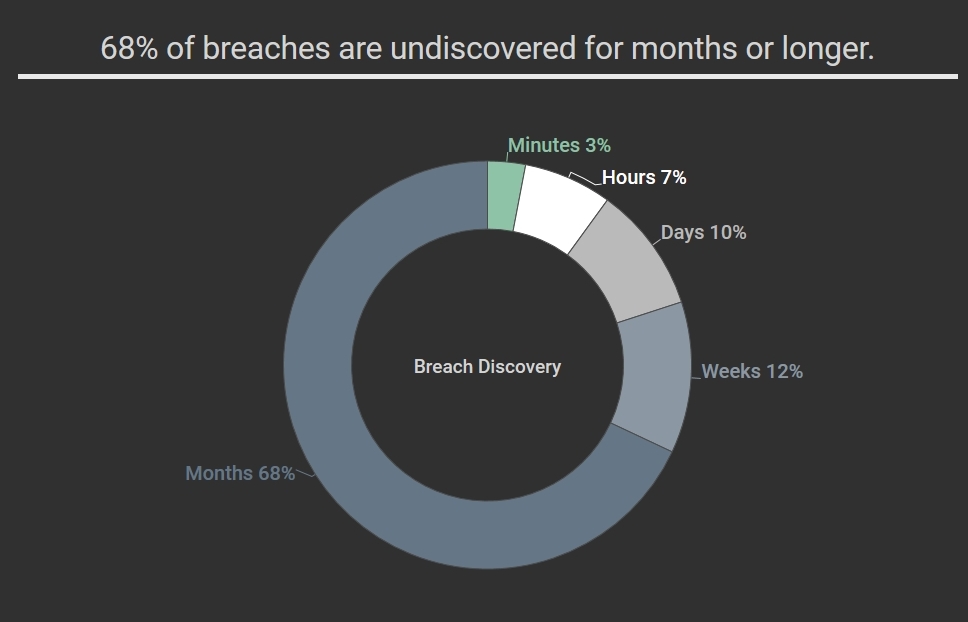
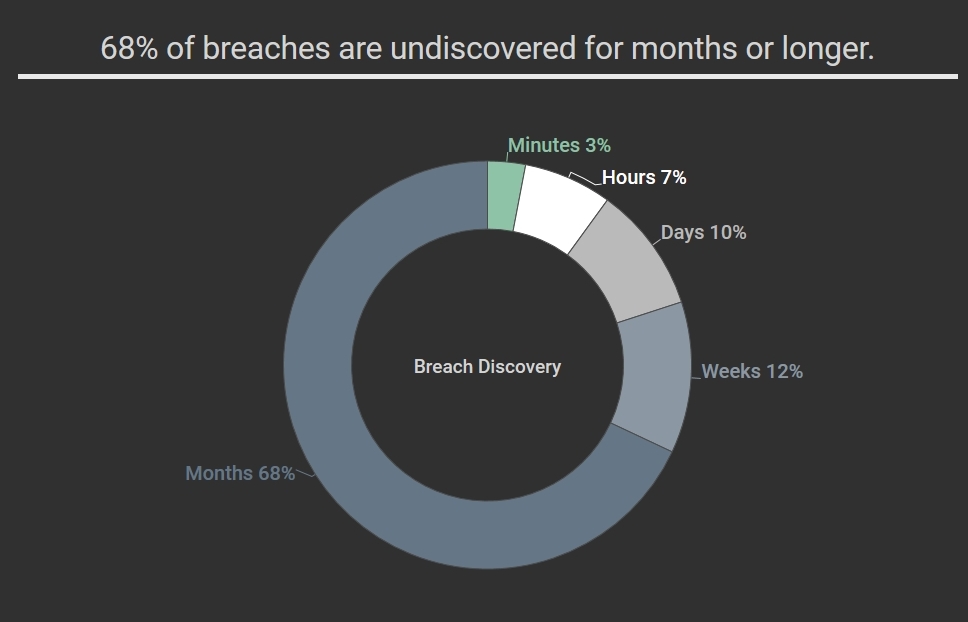
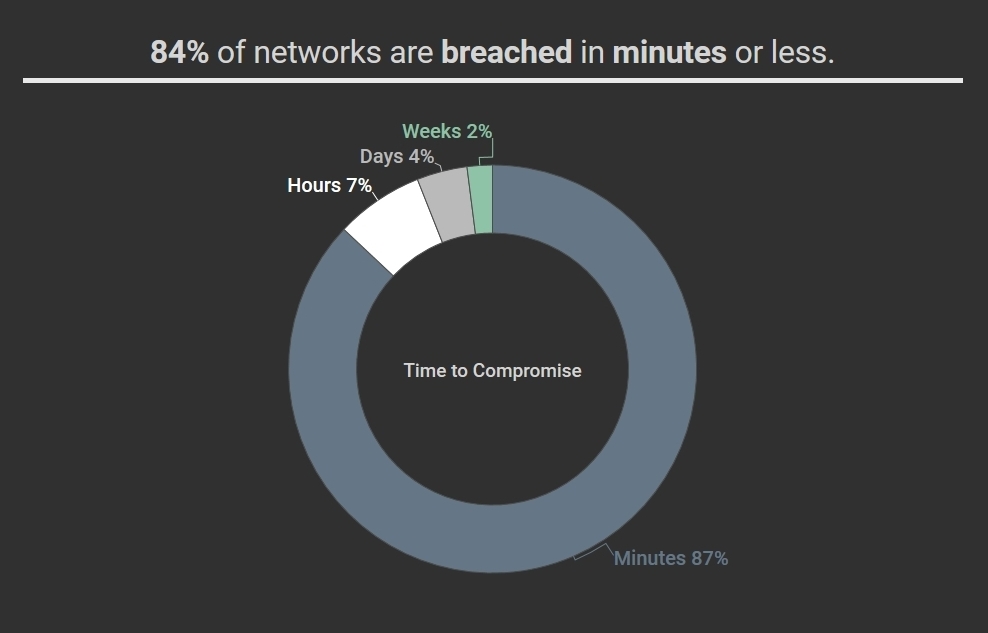
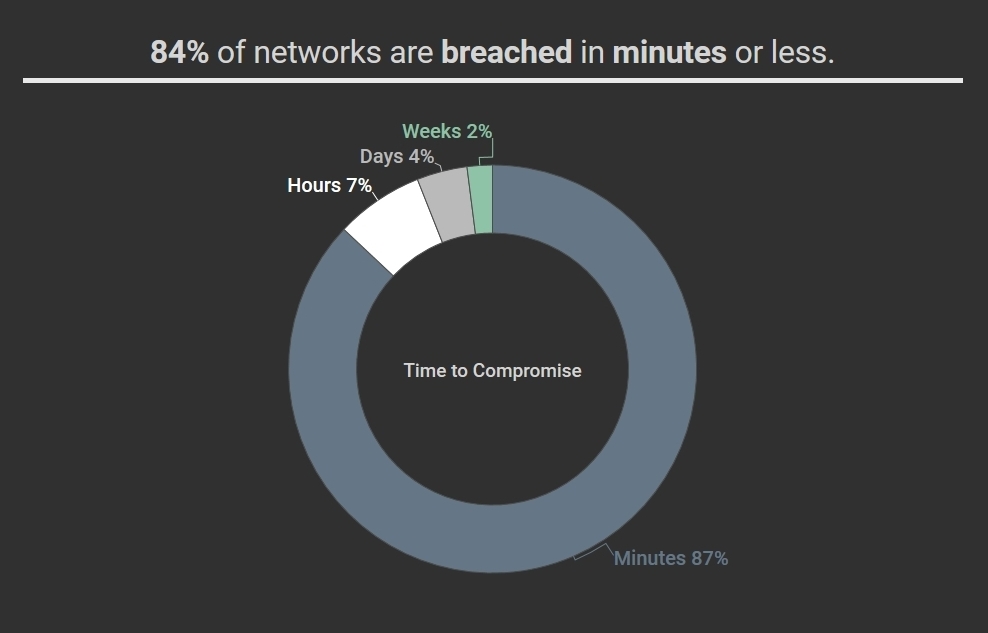
Cyber criminals are giving executives and IT departments sleepless nights. And the worries are increasing with frequent news of data breaches and ransomware. We want to help you fortify your network and educate your staff.
We do more than just harden and test your network and communication systems. We assist your organization in developing an integrated security posture that is built around a knowledgeable workforce.


DefenseCraft
Cyberspace is dangerous. We can help.
[zc4wp_sa3]
“It takes 20 years to build a reputation and few minutes of cyber-incident to ruin it.”
Stephane Nappo, Global Chief Information Security Officer at Société Générale International Banking